Ransomware attacks.
Imagine you start your day as usual, opening your computer to access your family photos, important work files, or even your monthly budget, only to be surprised by a large message that covers the entire screen. This message doesn't tell you that there's a technical error, it simply tells you: all your files have been encrypted, and you won't be able to access them unless you pay a sum of money. At that moment, you're not the victim of a hardware glitch, you're the victim of one of the most dangerous cyberattacks of the modern era, ransomware.
The digital world has turned into an invisible battleground, where thieves no longer need to break down doors or climb walls to steal you, just send a small link or seemingly innocent file to be able to take control of your digital life. In this article, we'll take you on a simplified journey to understand together what this software is, how it works, and how you can protect yourself and your family from falling into the trap of this digital thief.
What is ransomware.
Quite simply, ransomware is a type of malware that hackers design with one goal: to blackmail. The word ransom means ransom in English, hence the name. When this program manages to get into your device, it performs a process called encryption. Imagine encryption as putting all your files inside very sturdy iron boxes and sealing them with intricate locks, and the problem is that you don't have the key; only hackers have it. What sets ransomware apart from traditional viruses is its ultimate goal. Older viruses were often meant to sabotage the device or wipe data just for fun, while ransomware is an organized business that aims to make a profit. An attacker doesn't want to destroy your data, they want you to need it so badly that you're willing to pay money to get it back.
How does a thief infiltrate your digital home?
Some may ask: I'm so careful, how can this software get to me. The truth is that hackers rely on social engineering, which is a complex term that simply means to deceive humans. Here are the most popular methods they use:
-
First, the fraudulent email. You may receive a message that looks like it is from your bank, or from a courier telling you that you have a package waiting to be received. This message usually contains a link or attached file such as a PDF invoice. Once you click on the link or open the file, the malware starts working silently in the background without you noticing anything.
-
Second, suspicious websites and free downloads. When you search for a free copy of a paid program, or try to watch a movie illegally on untrusted sites, you open the door wide. Ransomware is often hidden inside these free files.
-
Third, security vulnerabilities. The software we use like Windows or browsers isn't perfect, and sometimes companies discover loopholes or gaps that hackers can get into. If you don't update your software constantly, you're leaving the window of your digital home open.
Moment of Attack: What's Happening Behind the Scenes?
Once the program enters your device, a race against time begins. At first, the program works completely silently — it doesn't want you to notice it until it's done with its mission. The program searches for the files that are most important to you: photos, videos, text documents, and databases.
Once it's identified, it starts encrypting them one by one. After it's done, the famous message appears on your screen. This message usually asks for a payment of hundreds to thousands of dollars. Interestingly, hackers ask for payment using cryptocurrencies such as Bitcoin, as these currencies are very difficult to track, ensuring that they can get away with their act without legal prosecution.
Sometimes, attackers add an element of extreme stress, such as placing a countdown counter that is clearly visible on the screen, telling you that the ransom value will double after 24 hours, or that the encryption key will be permanently destroyed, thus deleting your files forever if you don't pay within three days. This psychological stress is carefully considered; it aims to push the victim to make a quick and reckless decision under the influence of fear, preventing them from thinking calmly, consulting tech experts, or even informing the authorities. Moreover, some of these attacks have developed into what is known as double extortion. In this type, hackers don't just encrypt your files, they first steal a copy of them and transfer them to their own servers. They then threaten you, saying, "Even if you don't need your files because you have a backup, we'll post your sensitive data, your business secrets, or your private photos online for everyone to see if you don't pay." This development has made attacks more dangerous and harder to deal with, as the damage becomes moral, auditory, and not just technical.
Ransomware as a Service. One of the most
surprising and frightening things about this type of attack is that it has turned into a regulated business model. Experts call it Ransomware as a Service. In this model, professional groups of programmers develop the ransomware and equip it with all the necessary tools, and then rent or sell it to other less technologically savvy criminals in exchange for a percentage of the profits they make from the victims.
This means that the person attacking you may not be a programming genius, but just a user who has bought a ready-made tool from the digital black market. This shift led to an explosion in the number of attacks, as anyone with malicious intentions and a little money could start their own criminal enterprise, putting everyone, from individuals to small enterprises, in the circle of constant targeting.
Stories from the real world.
Ransomware is not just a threat to individuals, it is a nightmare for major organizations and countries. Look at the WannaCry attack that took place in 2017. This attack spread like wildfire in more than 150 countries in a few hours. Imagine that hospitals in Britain went out of business, and surgeries were canceled because doctors couldn't access patients' files. This attack has proven that cybersecurity is a matter of life and death.
Another recent example is the Colonial Pipeline attack in 2021, in which hackers targeted the largest fuel pipeline in the United States. This attack caused gasoline supplies to be disrupted, leading to long lines at gas stations and a state of public panic. The company was eventually forced to pay millions of dollars to restore its systems. These stories tell us that hackers don't differentiate between a simple individual and a giant company; everyone is a potential target.
How to protect yourself?
The picture may look bleak, but the good news is that ransomware protection is possible and simple if you follow a few basic rules. Here are the top tips to follow:
-
Backup is the golden rule: If you have a copy of your files on an external hard drive that isn't always connected to the internet, or on a reliable cloud service, the threat of hackers becomes worthless. If your device is encrypted, you can simply erase everything and restore your files from the backup.
-
Constant updates: Never ignore that message that asks you to update your operating system or software. These updates often contain security patches that plug vulnerabilities that hackers are trying to exploit.
-
Beware of digital strangers: Always be skeptical. If you receive an email from an unknown source, or even from a friend but in a strange way, don't click on any links or attach any attachments. Always check the source of the message.
-
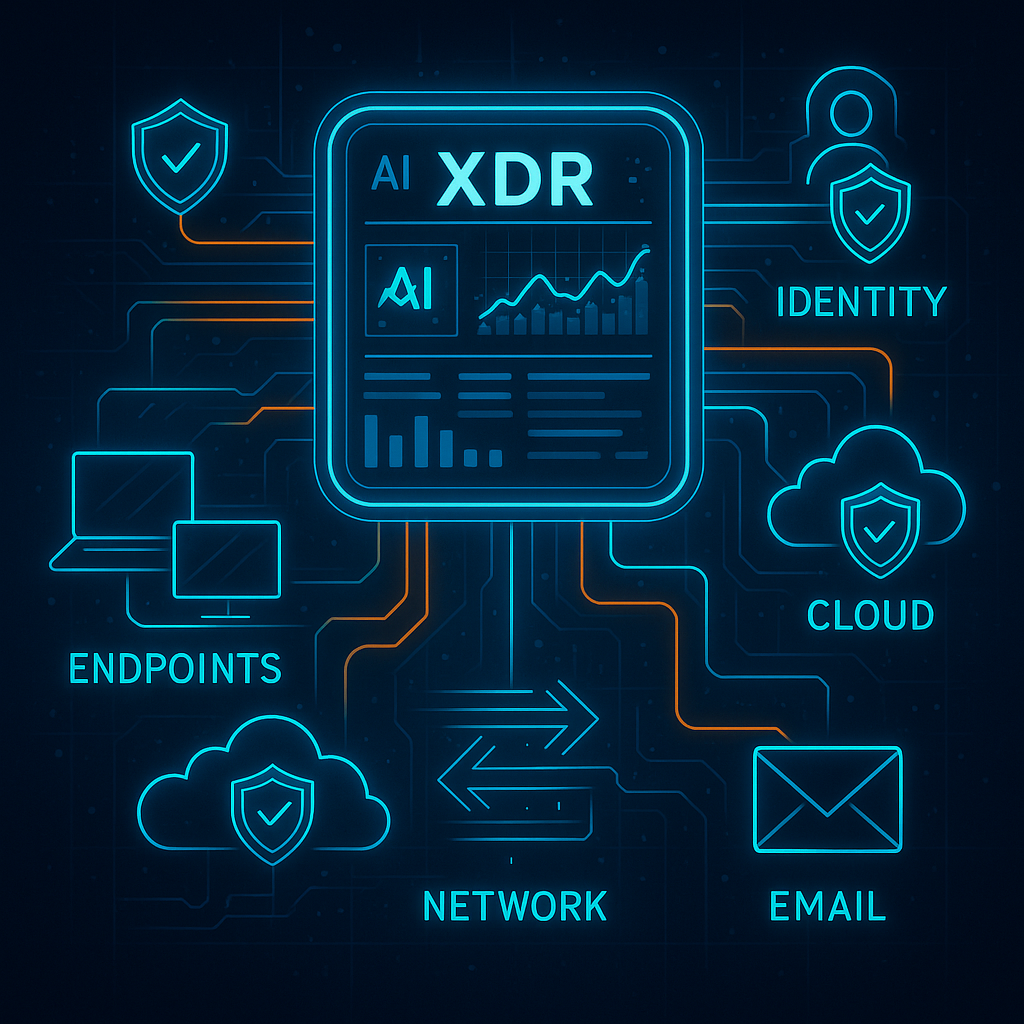
Use protection software: Make sure you have a strong and up-to-date antivirus software on your device. Modern software has the ability to detect and stop ransomware behavior before it starts encrypting files.
-
Two-factor authentication: Always use two-step verification for your important accounts. This means that even if a hacker steals your password, they won't be able to log in without the code that arrives on your phone.
What to do if you fall for a trap?
If you ever find yourself in front of a ransom message, the most important piece of advice is: don't pay the ransom. This may seem difficult, but paying doesn't guarantee you to get your files back; you're dealing with criminals. In addition, paying encourages them to continue their attacks and target other victims.
Instead, disconnect your device from the internet immediately to prevent the software from spreading to other devices in your home or business. Seek help from a professional technologist and look for free decryption tools provided by cybersecurity companies for some of the well-known types of ransomware. There are global initiatives like No More Ransom that provide free encryption keys to thousands of victims around the world.
It's not just personal devices, but it extends to smartphones, tablets, and even smart home devices connected to the internet. As our reliance on the Internet of Things increases, it has become possible for hackers to target any device connected to the network. So, a culture of security should encompass every aspect of our digital lives, from the smallest app on your phone to the largest database in your business.
In conclusion, we must realize that ransomware is part of the changing digital reality we live in today. Technology offers us enormous possibilities to connect, work, and create, but it also comes with new responsibilities and risks. The fundamental difference between a person whose digital life is destroyed and their memories or years of effort, and someone who survives an attack peacefully, is awareness and preparedness.
By following simple, yet crucial steps, such as periodic backups, conscious caution when dealing with everything unknown on the internet, and constantly updating systems, you can build an impregnable wall that makes a hacker's job nearly impossible. Always remember that your data and privacy are yours alone, and with a little care and knowledge, you can be sure that it will always remain safe and in your hands, free from the greed of digital thieves. Cybersecurity is ultimately not just a complex software or technology equation, but a culture of awareness and daily practice that begins with a decision by you to protect your own world. Investing a few minutes in securing your devices today can save you months of suffering and losses in the future. Be smart, be careful, and stay safe in this vast digital space.
 English
English
 العربية
العربية






Add New Comment